Network centric wars - readiness number XXUMX?
The concept of “network-centric war” was introduced by the vice-admiral of the naval forces of the United States of America, Arthur Sebrovski, and the JNS expert John Garstka back in 1998 year. This concept implies an increase in the combat and tactical capabilities of military formations in armed conflicts and modern wars due to the existing information superiority, as well as the unification of all forces and means participating in hostilities into one single network.
Then, as it happened according to tradition, journalists who specialize in military topics, John Archville and David Ronfeld, joined the idea. They set a goal to convince members of the US Congress that it is much better and more convenient to have a lot of cheap and simple combat platforms than a few expensive and complicated ones. The same principle applies to military units. Of course, in order for their activity to be effective, it is necessary to establish communication between these units and command posts - some kind of Internet. In this case, even a small platoon, the number of which does not exceed 50 soldiers, will be a very significant force, if this formation is connected with other forces and have network contact with at least a small number of fighter bombers.
The main principle of the conduct of hostilities in a network-centric war is the creation of so-called “packs”, and the enemy is supposed to be attacked in all directions with the help of small-sized units.
The idea has been under consideration since the 90-s of the last century. Already at that time, the level of development of radio engineering and space intelligence could provide troops with current data on the enemy forces. And the introduction of GPS systems into operation, as well as the intensive use of digital maps, made it possible to link them to specific locations and goals. New guidance systems were created, in particular, Tercom, as a result of which high-precision weapon. A huge number of means of electronic warfare made it possible to suppress the enemy’s control complexes, which led to disorientation. Therefore, practically the only thing that needed to be added was to link all these means using high-speed closed-circuit channels and to ensure data transmission over this network.
In case of successful creation of a global combat Internet, which can be used to transmit information in real time, such a system will allow to monitor and control all branches and types of troops from a single center. Thus, the new system will enable the Pentagon to directly control the situation anywhere in the world, where the Americans will decide to “establish democracy”. In addition, the President will have the opportunity to observe the progress of the battle on the computer monitor and, if necessary, contact the commanders.
The implementation of the complex of all necessary components is designed for 10 years. Therefore, it must be completed by 2020 year. It will be held as part of the creation of a unified information space. It was supposed that more than 200 billions of dollars were needed for the implementation of this plan, but now only in the ground forces 230 billions were spent on the implementation of these goals.
One of the results of the program should be the creation of a global information network, designed to provide information to all elements of the national security system of the state. This network has a service-oriented architecture. The network has a structure that provides information sharing not only within one type of armed forces, but also within the network information exchange between different units and types of troops. Thus, the Global Information Network is a kind of array of satellites in orbit that monitor the entire globe.
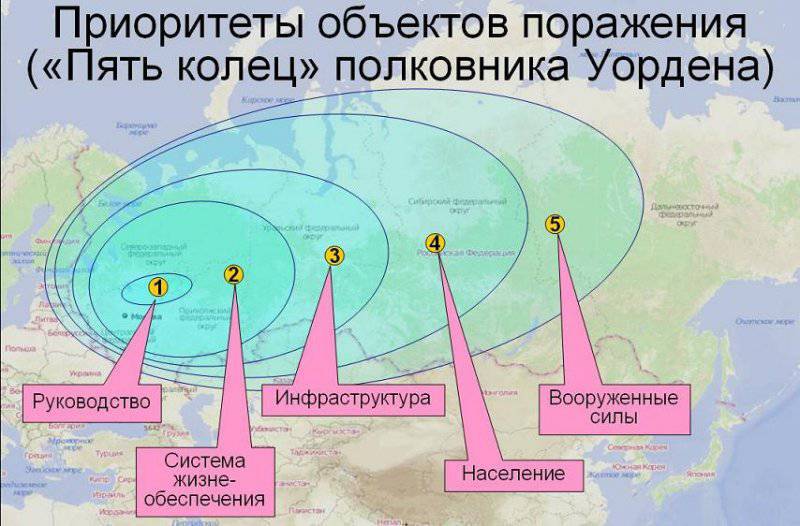
However, having enough information and precision weapons to strike is not at all difficult. The main thing - to determine where to hit. Therefore, in the theory of network centrism, there is such a thing as a system of priority goals, the essence of which lies in the system analysis of the victim state. This analysis is based on the concept of "five rings". The main goal is, as a rule, a political leader who needs to be destroyed (not literally, not physically, but psychologically, forcing him to renounce power or leave the country). Next - the industrial and energy complex of the country. And only at the last position are the national armed forces, because with the correct implementation of the concept with them, it will not be necessary to fight, the revolution will automatically break out in the country. Vivid examples of using the ideas of the network-centric war and the concept of the "five rings" - Libya, Iraq, and now - Syria. The processes and schemes are the same everywhere, and the scenarios for the seizure of power in these countries are worked out almost to absolute perfection.
The American military-political elite does not stop at bribing the enemy’s command. This is more profitable, and the loss is less ...
Thus, the idea of a network-centric war is more a mental-philosophical concept than a technical one (if, of course, to consider it in the context of the foregoing). Readiness for this kind of war is determined by the state of speculation of the military leadership, their ability to turn the decision-making process of opponents in a direction advantageous to themselves.
But if we consider technology and consider the system from the point of view of military use, the idea of network-centrism is a concept of control, not of conducting combat operations, that is, in essence, this system is a reflection of technological approaches to the problem of implementing a single command of the US armed forces.
But there were quite a few high-ranking officials in the country who opposed the system of network-centric wars. Some opponents strongly doubt that the system will be sufficiently effective, that it can be used in various kinds of conflicts, in particular, in the conditions of urban combat. According to others, excessive hope for high technology can cause system vulnerabilities, because technology can fail. In addition, there are other problematic issues, in particular, whether the information systems of the coalition troops will be compatible, whether the frequencies will be sufficiently capacious for network-centric operations, how to get out of the situation in case of unforeseen situations.
The starting point of the beginning of criticism was the not-too-successful use of the system during the first Iraq war. Recall that in April 2003 between the American troops and the Iraqi army there was a battle for the bridge that crossed the Euphrates River. This bridge was the last obstacle for Americans on their way to the capital. But it was this place that almost turned into a military grave for American soldiers, and more likely a miracle than computers saved them from destruction.
And it all started quite normally. The soldiers were tasked with capturing and holding a large bridge southwest from Baghdad until the main forces approached. Before the start of the operation, the intelligence carefully examined photographs taken from satellites, reported that the bridge was not guarded and no enemy troops were observed in the vicinity. Therefore, the battle on the approaches to the bridge was an unpleasant surprise for the Americans, who were forced to hold the defenses for a day and repel counterattacks by Iraqi forces, which totaled about 8 thousand people and about 70 armored vehicles and tanks.
But the American troops were equipped with systems that are planned to be used in the network-centric war. And how did such a perfect system not find a cluster of quite a large number of people and equipment? The comments of the Pentagon on this issue sound all the more strange: the task force was moving so rapidly that it overtook the intelligence service ...
The US Army was armed with a system called the Blue Force Tracker, with which you can mark the alignment of forces on the battlefield. This information should be up-to-date and up-to-date. The system resembles a computer game: on the monitor, all the troops that take part in the battle are indicated by icons, moreover, their forces are marked in blue, and the enemy forces in red. These icons must be moved manually by intelligence officers, using the information received from satellites and drones information.
But since the blue icons remained in place, the commanders suggested that the red ones should also be static, but in fact this was not at all the case. In practice, there was also little order. Despite the fact that the headquarters knew about the presence of Iraqi troops in the area of the bridge, the commanders on the ground did not see a single enemy unit on the monitors.
Later, during a discussion of failures in Iraq, the American command, which believed in the effectiveness of the network-centric system, announced that the program and architectural flaws of the system were to blame. Intelligence officers also confirmed the information that the system turned out to be practically useless, because the information came in extremely slowly, which negatively affected the speed of decision-making. If there was a need to get new data, we had to stop, deploy a huge number of antennas, and thus establish communication with the army mobile communications system.
Some critics of the system claimed that it is suitable for conducting combat operations and conducting operations at sea and in the air, but it is completely unacceptable for the ground forces. In particular, the American General Scales, already retired, said that the idea of a network-centric system, implying the creation of an all-seeing eye in the sky, turned out to be a failure in practice and had to spend hundreds of billions of dollars for this failure.
If we talk about open sources of information, it should be noted that recently in the American press there are less and less publications on network-centric wars. And those that can sometimes be seen are more and more critical. According to experts, in the American military strategy, too much space is given to innovative technologies, and in fact the hopes that they will help on the battlefield are untenable, not supported by a sufficient base.
According to the representatives of the Pentagon themselves, soon they will have to engage in battles with irregular troops, so the answer to the question: “Will the network-centric system in any new way be effective in new conditions?” Is obvious. Moreover, hostilities in Iraq and Afghanistan have demonstrated that it is impossible to rely on technology in an environment where enemy forces are mixed with civilians.
Thus, if we talk about the “peaceful” version of the use of the network-centric system, then it has long proved its effectiveness and soundness, but this is not yet possible to say about the “military” version. Progress, of course, is very good, but the idea of network-centricism during the conduct of hostilities can have not so much a positive as a negative impact, cause a decrease in the level of necessary knowledge, and also disorient commanders in real combat sites ..
With each new century, war is changing. And if before its main feature was the use of weapons, then at the present time for the start of the war it is enough to have a strong psychological and mental impact on a certain people, and then he will do everything that is needed. War, therefore, is not always physical violence, it is a zombie consciousness of the population with the help of information technology, which leads to the emergence of aggression. There is no need to go far for examples: gas war, cheese war, war of compromising ...
Materials used:
http://www.itogi.ru/exclus/2012/17/176984.html
http://www.milresource.ru/NCW.html
http://globalismtv.narod.ru/setetsentricheskaya_voina/
http://yablor.ru/blogs/setecentricheskaya-voyna/2413871
Information