Cipher Day in Russia
At the same time, cryptography appeared long before 1921, including in our country, experts call it one of the oldest sciences in human storiesThe age of cryptography is estimated at several thousand years. Cryptography is the science of methods for ensuring the confidentiality of data transmission; it ensures that it is impossible for unauthorized people to read important information, often representing state secrets. Initially, cryptography was mainly focused on the development of data encryption methods - reversible transformation of the original textual information based on an existing key or a secret algorithm into an encrypted text that an unprepared person could not make out.
History of cryptography in Russia
The first mention of the emergence of cryptography in our country dates back to the era of the reign of Ivan the Terrible. It was then that the first “professional cryptographers” appeared, who worked in the Ambassadorial Order created in 1540. The ambassadorial order in those years was responsible for the foreign policy of the state. Employees working in the order created the so-called "tsifir", "alphabet" or, more simply, ciphers, as they will be called later. Initially, these were ordinary replacement ciphers.
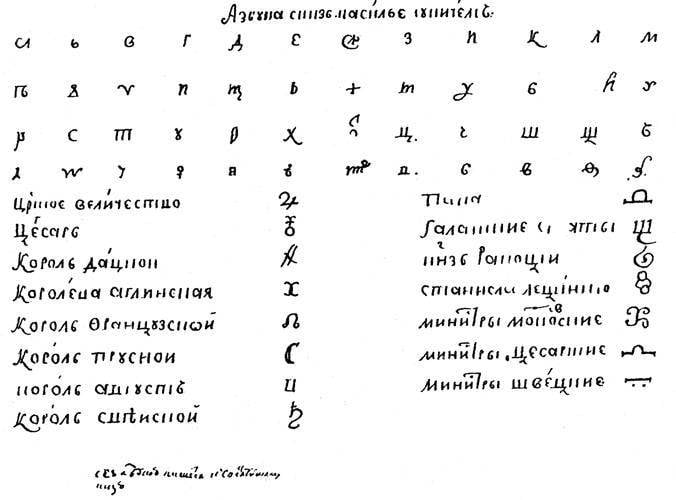
But the full-fledged emergence of cryptography in Russia occurred later in the era of the reign of Peter I, who realized the importance of this science for the security of the state. It was during the first Russian emperor that the cryptographic service became truly professional. Starting from 1700, all the necessary work on encryption and decryption, as well as the creation of new ciphers, was carried out by employees of the digital section of the Ambassadorial Order, and later - from 1709, the Embassy Office. In those years, the cryptographic service in the Russian Empire was under the constant supervision of two important officials - the state chancellor Gavril Ivanovich Golovkin and the vice-chancellor Peter Pavlovich Shafirov. They also heard incoming reports of intercepted foreign codes. Theoretically, this can be considered the beginning of a full-fledged cryptanalytic activity in our country. At that time, a simple replacement cipher was considered a typical and common cipher, when each letter of the alphabet was replaced by a new letter, sign, or combination of letters. Also, “dummies” - meaningless characters could be added to the text.
Up until the first half of the 19th century, the vice-chancellor oversaw the cryptographic service in Russia. Gradually, professional mathematicians and cryptanalysts began to take service. One of the largest Russian cryptographers of the first half of the XIX century was the famous scientist Pavel Lvovich Shilling, the inventor of the first ever electromagnetic telegraph. From the beginning of the XIX century, the service of cryptography and perusal (secret opening of correspondence) was transferred to the Office of the Ministry of Foreign Affairs, the ministry itself was formed only in September of 1802. Schilling, who had been in charge of the digital expedition of the Ministry’s office since 1818, developed a bigram code. When using it, not individual letters were encrypted, but their double combinations, digrams. It was helped to get rid of the statistical dependence by the fact that letters that were at a great distance from each other could unite with each other.
The second half of the XIX century was the starting point for the expansion of cryptographic functions between various ministries. Cryptography has ceased to be the prerogative of the Ministry of Foreign Affairs, appearing in the Ministry of the Interior and in the military department. The value of cryptography in the state life of the Russian Empire only increased. But the entire country and the army, including the Russian cryptographic services, turned out to be insufficiently prepared for the First World War. Reliable wire telegraph communication between the parts was almost completely absent, and the interaction between them was carried out via radio communication, but there was simply no existing mechanism for encrypted radio communication. Often all information was transmitted in clear text. It was in this way that the headquarters of the Samson and Rennenkampf armies communicated during the offensive in East Prussia. The interception of these talks led to the catastrophe of Samsonov’s army in East Prussia, the two central corps of the 2 Army were surrounded and defeated, and General Alexander Vasilievich Samsonov himself shot dead.

Unfortunately, the Russian imperial army lost the war on the air. This was facilitated by the violation of the rules for using ciphers, poor organization of encrypted radio communications (some parts could get a new cipher, while others still used the old one) and the weakness of the ciphers chosen. The shortcomings of the Russian army of those years also attributed the lack of special decryption units that France and Austria-Hungary had before the war. After such offices in Russia were created, they faced a shortage of means of direction finding and interception of radio messages, this once again proved that Russian industry was not ready for war, which, contrary to expectations, turned into a protracted world conflict that buried European empires, among which was the Russian Empire.
At the same time, Russian cryptographers also had some success during the First World War. The decryption service of the Ministry of Foreign Affairs worked well before the war and in the first half of it, allowing the employees of the ministry to get acquainted with the diplomatic correspondence of European states. The most successful operations of the newly emerging military interpreters included the quick opening of the German naval cipher, which made it possible to read the orders and messages of the enemy. Signal books and other important documentation were captured on a stranded German light cruiser Magdeburg. At the same time, a special operation was carried out, so that the enemy thought that the books were in fact destroyed and did not change the cipher used in the Navy.
Cryptography during the Great Patriotic War
After the revolution and the completion of the most active phase of the civil war 5 in May 1921, a special department was formed at the Cheka, which specialized in the management of cryptographic affairs. So the encryption service survived its rebirth, now in Soviet Russia. The department was headed by a revolutionary, an ally of Lenin and a nobleman by birth, Gleb Ivanovich Bokiy. Born in the family of a full state councilor, Gleb Boky already in 1900 joined the RSDLP, linking his life with the revolutionary struggle. The first success of the new service happened in the same year, 1921, when the German diplomatic code was decrypted. From that moment until the end of 1933, the correspondence of many German diplomats and consulates in the Soviet Union was controlled by the Soviet side. But the fate of Gleb Ivanovich was tragic. In the 1937 year during the “Big Terror” he was arrested and shot, rehabilitated in the 1956 year.

Even before the war in the USSR, secret communication lines (telegraph and telephone) and cipher machines were widely developed, on which many Soviet research institutes, both civilian and military, worked. Back in 1930, the first two HF communication lines (high-frequency communication) between Moscow and Leningrad and Moscow and Kharkov were launched in the country. In 1935-1936, a special device for automatic classifying telephone conversations was developed, called the EU inverter (by the names of the creators of Egorov and Staritsyn), and the release of this device for HF lines was established. Without such equipment, HF communication could only be protected from direct listening. By the 1941 year, the 116 RF stations and 39 broadcasting points were already operating in the Soviet Union, and the total number of subscribers among the leaders of the state and the party leadership of the country reached 720.
According to the recollections of Marshal Baghramian, no high-frequency communication was carried out during the war and no significant operation took place. In the management of troops, she played an exceptional role in facilitating the implementation of the tasks set by the command. Already in the first period of the war in the USSR, the models of the SI-15 “Sinitsa” portable equipment and the Snegir SAU-16 portable saucer were developed, the devices were made in the form of a suitcase. This equipment was used by the high command when traveling to command posts that were not equipped with high-frequency communications stations.
Particular attention was paid in the USSR to the development and production of encryption machines, the first of which went into mass production as early as 1938. For example, the cipher machine M-100, which could not boast of low weight - 141 kg. Only the batteries to it weighed 32 kg. This technique was successfully used in the pre-war period during the battles with the Japanese on Khalkhin-Gol and in the Soviet-Finnish war of 1939-1940. Such equipment was widely used in the link of the General Staff - the army headquarters. Later, more compact encryption machines appeared in the country, for example, the M-101 "Emerald" and K-37 "Crystal".
In the years of the Great Patriotic War, the main encrypted communication of the machine took place during the transmission of various secret telegrams, and the Soviet cryptographic service managed this task perfectly. In the 8 Office of the General Staff of the Red Army during the war years, more than 1,6 millions of encrypted telegrams were processed. The eighth directorate of the General Staff exists in Russia to this day.
The current state of the military cryptographic service
After the end of the Second World War, encrypted communication was finally established as the most reliable type of hidden communication used by the Soviet armed forces. Such a connection was used primarily to convey the most important information that required a special degree of confidentiality and related to a limited circle of people. Since the end of 1970-ies, the cryptographic service has begun to develop new measures aimed at the security of information transmission in automated command and control systems, as well as in computer centers created. Over time, the value of cryptography and encryption only increases, and the volume of information transmitted daily, including those representing state secrets, is constantly growing.
Protection of state secrets in the Armed Forces of the Russian Federation lies on the shoulders of the staff of the Eighth Directorate of the General Staff of the Armed Forces of the Russian Federation. The constant increase in the high-tech and science-intensive component and the emergence of new threats and challenges in the field of information security require today the application of applied scientific and fundamental approaches to organizing and ensuring the protection of information representing state secrets. Especially for these purposes in Russia in 2014, a research center was established as part of the Krasnodar Higher Military School named after General of the Army Sergey Matveevich Shtemenko, the main task of the center is to conduct research work in the field of information security. It is worth noting that this military university is the base for the training of military information protection specialists. In the same year 2014, a scientific company was formed as part of the school, in which the most talented graduates of civilian Russian higher educational institutions are engaged in conducting scientific research in the interests of the Armed Forces of the Russian Federation.


Information