Digital Cyber Shield
Questions about the creation in Russia of an analogue of American cyber command periodically get into the media. According to sources of the Russian agency Interfax, which are familiar with the situation in the Russian Defense Ministry, at the first stage of its development, this structure will function as the main department of the Russian Defense Ministry, acting as part of the East-Kazakhstan region troops. Gradually, the list of tasks that Russian cyber command will have to solve will emerge.
For example, in an interview with Russia 24 channel, Russian Deputy Prime Minister Dmitry Rogozin, who oversees the development of the defense industry, noted that the unit that is being created to ensure Russia's security in the electronic environment, along with reflection and protection from cyber attacks, will also be engaged in developing Russian BY. As Dmitry Rogozin noted, if all the software is imported, we simply will not know what may be in this “black box”, in this case it will be impossible to say anything about cybersecurity. From the lips of Russian officials sound quite serious statements. But how to solve the problem with the selection and training of specialists, and most importantly, with their retention at work in government agencies, is still not entirely clear.

The terms of the Russian cyber command formation were called different: until the end of the 2013 of the year and in the 2014 of the year. Now, apparently, the final date of their formation will be 2017 year. According to the 2017 year, according to the Chief of the 8 Department of the General Staff of the Russian Federation, Yuri Kuznetsov, the Ministry of Defense expects to create a special structure designed to ensure the security of military facilities from various computer attacks from the outside. According to Yuri Kuznetsov, work in this direction is carried out in stages and should be completed by 2017 year.
Recall that a year ago, Russian President Vladimir Putin signed a decree "On the creation of a state system for detecting, preventing and eliminating the consequences of computer attacks on information resources of the Russian Federation." This system was supposed to be one of the structures of the FSB. In the summer of 2013, it was reported that the Russian Ministry of Defense plans to create in the country a separate branch of troops to effectively combat cyber threats. These troops were to be created by analogy with the American cyber command and engage in the fight against cyber threats and monitoring and processing information coming from outside. Dmitry Rogozin wrote for the first time about the creation of his own cyber command in Russia back in March 2013.
It is worth noting that the emergence of a separate cyber security structure within the Russian Defense Ministry is quite a logical continuation of the modernization of the entire national information security system of our state. In particular, the emergence of this structure in the Russian Armed Forces contributes to the gradual transition of our army to military equipment, armaments, and combat control systems with a very high proportion of modern digital components, said Yevgeny Yushchuk, who is an expert in competitive intelligence.
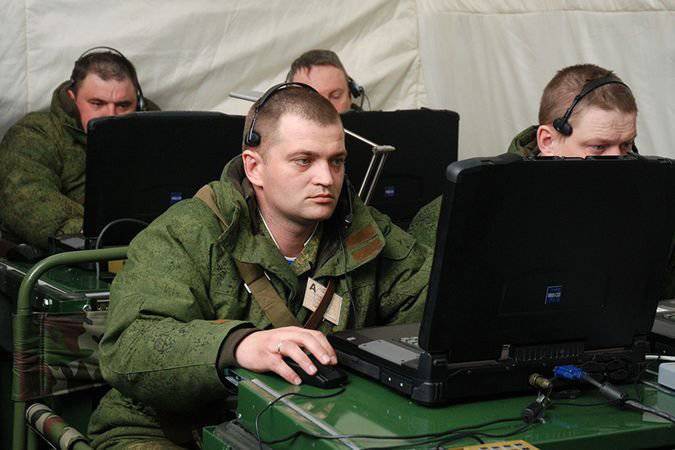
Yuschuk notes that, looking at photos of any modern exercises of our army, you can see a large number of laptops that are protected from dirt, shock, dust, combat control systems, which are based on modern computer technology, etc. Nowadays there are many so-called smart systems that are able to coordinate the actions of units and individual soldiers on the battlefield. So, if these systems exist today and are actively used, then there will be attempts to hack them. In particular, information has already appeared about how the Iranians managed to intercept the American UAV, simply hacking into its system and taking over control.
How exactly the new Russian structure of cyber defense will look like, the experts still find it difficult to answer, which is explainable in principle, since such systems can most likely be classified as state secrets. But the approximate composition of the components and the list of objects that need protection can be predicted. This, in particular, was taken up by Viktor Litovkin, executive editor of the popular newspaper “Independent Military Review”. According to him, the structure being created in Russia will consist of a number of layers of cryptographic, technical, electronic protection, as well as a large number of other systems that can duplicate each other, as well as protect critical structures for the Russian Defense Ministry. First of all, we can talk about control points for various types of weapons, especially the Strategic Missile Forces, anti-missile and air defense systems, main headquarters and command posts.
At the same time, Litovkin stressed that a certain element of protection against cybernetic threats exists in the Russian army quite a long time ago - unlike the armies of some foreign states. For example, none of the channels of transmission of official information of the Ministry of Defense of the Russian Federation has access to the Internet, which, in turn, significantly reduces the possibility of a potential adversary to conduct cyber attacks.
As Sergey Oznobishchev, a member of the Council on Foreign and Defense Policy, noted that today, heightened attention to cybernetic threats is a feature that is characteristic of all developed armed forces in the world who show proper care about their military power. This threat is natural enough and easy to understand - this is the kind of impact that can completely or partially disable entire systems of modern armaments, the Strategic Missile Forces, cause disruption of interaction on the battlefield. That is why today each country decides for itself on what scale to deal with this problem, understanding that this problem is serious enough, which means that it needs appropriate attention.
Information sources:
http://rus.ruvr.ru/2014_02_02/Minoboroni-formiruet-cifrovuju-zashhitu-5309
http://eurasian-defence.ru/node/26569
http://finam.fm/read/11578
http://polit.ru/news/2014/01/30/defence
Information