Satellites, tanks and AI. Augmented Intelligence
AI for military purposes or, as some call it, augmented intelligence
There is so much confusion in the first parts. So much at first glance different and absurd at the same time. Incomprehensible satellites, strange Tanks with electronic filling, in the title there is a hint of a voice assistant from Yandex or Sberbank. Now I will connect all the parts in order. I will disappoint you right away: there will be no talk of any “Terminators” or Skynet. The consideration will be what is available and what you sometimes have to deal with, well, and a little imagination based on really available developments.
What do we know about neural networks and AI based on them, where do we meet with them?
Usually these are annoying voice assistants in the support services of banks, insurance companies and mobile operators. Alice, Marusya, Alexa from the same opera, only better. What else can they do and where can you encounter them? Those who drive a car and accelerate above the allowed speed receive chain letters with recognition of the make and number of the car. The system was finished to the level that it distinguishes well between splattered car numbers in a dense high-speed stream.
Soon there will be a system that distinguishes between the busiest business people in the world who just urgently need to talk on the phone while driving, and a system that captures the throwing of garbage from cars. I look forward to a system that distinguishes between humanoid individuals with erroneous DNA that throw cigarette butts out the window or balcony. The use of AI to combat this dead-end branch of human development is more than justified.
Comic and not so videos with the replacement of the main characters with other characters are no longer as surprising as before. For such tasks, solutions based on neural networks are most often used. Deepfakes and the generation of pictures of naked girls based on a text description are from the same series. The most realistic three-dimensional models based on a text description with subsequent printing on a 3D printer are on the way. After that, you can rightfully consider the future to have come.
What else can be presented as examples, besides neurons, for the complete exposure of girls in photographs in swimsuits? A bunch of financial tools for predicting market behavior, trading Robots for high-frequency trading on stock exchanges. Actually, where did all these things go to the masses. In some banks, the decision to grant a loan is no longer made by a girl with a calculator and 1C courses, but by an AI-based system.
Based on the analysis of your electronic payments, they are able to predict the level of credit confidence in you with a certain accuracy. Branch prediction and data prefetch systems in modern processors. All kinds of speech recognition systems, images, patterns of behavior. Many complex problems are modeled with the help of genetic algorithms. And often the output is very strange, but working solutions.
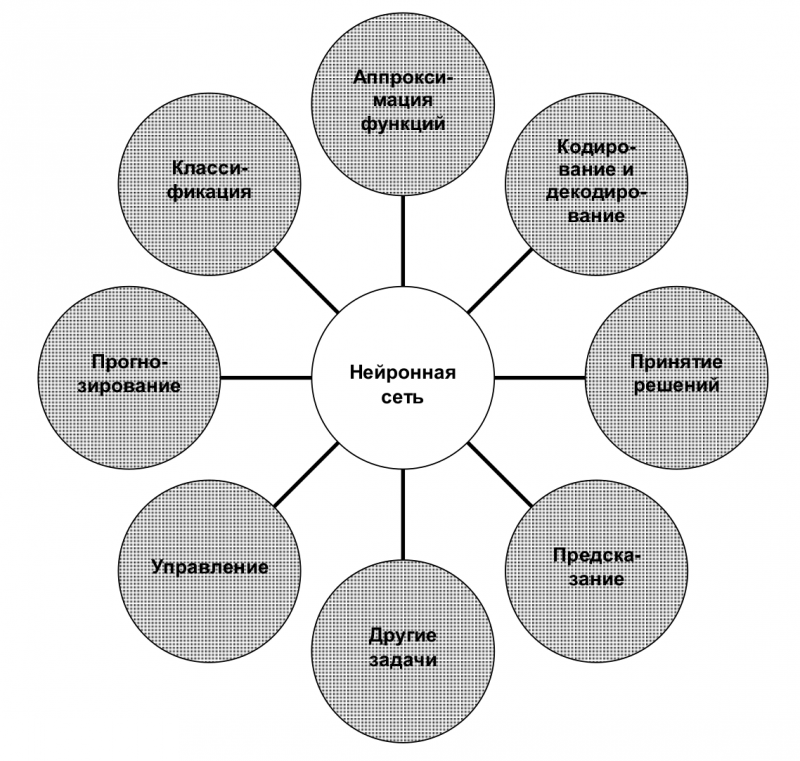
The relevance of the use of AI based on neural networks increases many times when it becomes necessary to solve poorly formalized tasks. Together with the ability to process and analyze huge amounts of data, this allows you to calculate options for a large number of variables. At the same time, there is no influence of the human factor, that is, it is independence from the mood, personal problems and emotions that are inherent in people. The main tasks that can be given to the mercy of artificial intelligence are in the plane of accelerating decision-making and automating routine processes.
For what purposes is the use of neural networks and AI based on them justified?
1. Pattern recognition
In social networks, many have seen or have long been using the ability to recognize faces in photographs. You upload a photo from a party, the social network selects happy faces in rectangles and offers to indicate participants from among friends on them. Then she automatically begins to recognize them in the following photographs, then completely guts the entire photo gallery and finds drinking buddies there in other photographs, which very much resembles a wife or mother. And if earlier there were certain problems with recognition, now the AI of the social network determines exactly where the cat's face is and where the owner's face is. Even when the cat's is much better and more pleasant than the owner's.
With image recognition, their classification in photographs and videos, social networks can easily cope with a huge influx of users. It’s hard to say how many thousands of photos a particular social network shovels every second, because people upload photos and videos quite often. Some continuously.
Now back to optical reconnaissance satellites.
Here they are uploading photos and videos from the battlefield in real time. They need to be processed somehow, looked through, find the necessary objects, classify them, if necessary, take the materials received yesterday or the day before yesterday, and compare in order to understand what the enemy has done there.
This is where the fun begins. Who will take care of this routine?
There is a lot of data, and they are heterogeneous, and the human visual channel is rather weak for these purposes. You have to carefully look through the square after the square, remember and compare with what was on the previous squares, remember what happened yesterday.
This is not at all like watching a demobilization album. In this case, you must act quickly and very carefully. Only the eyes are not made of iron, they are characterized by fatigue, the brain can also get tired of such work, although the possibilities of the human visual cortex are fantastic. And this is one of the troubles. The human brain easily draws what is not there. Computer vision developers will confirm this for you.
On the other hand, train AI for certain images, teach it to process data from different ranges of the electromagnetic spectrum and let it thresh itself, recognize fortifications, equipment, fighters. Pull up if needed historical data for yesterday, the day before yesterday, from last week and compares with those already available. On finding objects and suspicious things informs the operators, and they make decisions.
For these purposes, huge data centers are not needed, because several dozen “Instasams” upload much more data in high-definition videos and photos processed with ennobling filters into their public pages than our satellite constellation.
Accordingly, the question is brewing, where to get such data centers? Preferably mobile. Well, so that they can get away from the enemy dronescreated back in the Soviet Union.
Most likely, they will have to be taken in the same place as domestic video cards, processors and high-definition monitors or solid-state drives. There is no listed element base in washing machines and microwave ovens. Even buying something old is a problem. The same neuromorphic IBM chip developed in 2014, go and try to find it.
It is necessary to fence a chain of mediator countries and try to please them so that they do not accidentally remember that they can suffer for mediation. You will have to develop a lot from scratch. And this is a rather long and costly process, taking into account the fact that we do not have not only such a number of specialists, there are not even theoretical groundwork in science. For more than 30 years, we were very willing to do nothing but buy high-tech developments, and with an open soul, at best, we sold for pennies, or even gave away just like that as unnecessary.
I will not sing odes to gallium/indium arsenide again. Judging by the latest observations, technologies based on it are being developed and developed in the countries of Southeast Asia. It is possible that those cunning to the perspective and breakthrough guys will reach the research work of Vsevolod Sergeevich Burtsev on discrete optical computers.
Perhaps we will soon see computing systems based on other physical principles. For 30 years, photonics, microelectronics and technology have advanced quite far, and now much is real that could not advance further than theoretical developments before. Or lack of funding and any interest, as in our case. And we, as always, will try to copy in haste and try to catch up with the rushing train.
Nevertheless, the task of pattern recognition is feasible with our current capabilities, despite all external limitations. For the operation of neural networks, cascades of video cards are usually used, comparable to mining farms. After the turmoil in the cryptocurrency market, there is an excess of video cards, in the secondary market there is a blockage in some places. Of course, we don’t see computers from nVidia directly specialized for such purposes, but we are quite capable of assembling a cluster of commercially available video cards for AI that recognizes images.
2. Forecasting ambush sites
Murphy's Laws of Combat say that professional soldiers are predictable, and the biggest danger is unpredictable amateurs. Training of professional military takes place according to certain standards using specific methods. Techniques systematically drive in a certain model of behavior in a given situation. And so for a long time. Only amateurs improvise.
In addition, any initiative in the army is severely punished, especially in ours, and indeed any domestic civilian will say that, as a result, the initiative strongly loves the initiator. As a result of these factors, a certain pattern begins to be traced in the actions of the military. In machine learning theory, this is called behavior patterns. If in a simple way, then templates. Often noticeable even in everyday life.
This is especially true for our military. Since the fundamental basis of the combat training of the domestic military is marching in step and singing songs in chorus on the move or on the spot. It is enough for the enemy to turn on “Travel March No. 1” at full volume, as, according to the conditioned reflex developed by many years of training, our fighters will begin to stagnate and pull their legs with a go-ahead. Reflexes will work, and they will not be able to do anything with themselves.
The apologists of this pedagogical method are blindly sure that in this way an invisible telepathic connection will be established between colleagues at the quantum level, which cannot be drowned out by any electronic warfare on radio tubes with a radioactive cathode. Otherwise, one cannot explain the antediluvian state of the means of communication in the troops, which are irrevocably lagging behind civilian models. Someone has to object?
I will answer using the example of a twenty-year-old Sony Ericsson T100 phone. Already in those years, the radio module of this simple and compact phone automatically tracked and selected the appropriate cell tower according to the signal level, jumped over frequencies and channels when switching between base stations without manual intervention. Audio codecs provided sufficient sound quality, while compressing the signal, providing noise immunity and speech masking.
It had a graphic display and a very user-friendly menu. Over the years of work, he has experienced more than one fall, flights of the body from a bicycle and with a bicycle, many days of forty-degree heat and twenty-degree frosts. The only consumables were batteries and SIM cards. It is still in working order. Now give an example of a similar one from the modern in the domestic military mobile communications. Such is the ambush with the connection we have.
Let's get back to armed ambushes.
Any ambush made according to the canons (read - patterns) of military art is usually done according to certain rules and has specific restrictions. Restrictions limit the possible options for the applied weapons, the size of the ammunition load and the number of fighters. Well, a professional in his right mind and intelligible mind will not ambush in an open field from a howitzer with five shells and a platoon of unarmed soldiers. Although the unpredictable domestic history keeps a lot of such examples, and modern too, and cases with an unarmed column in an open field without cover and at least some kind of support in general have become textbooks.
With modern means of observation, this absurdity will be detected quite quickly from the air or space, and then they will be quickly butchered from the ground. A professional sniper will not hide on a children's swing or carousel, unlike a crazy amateur. Due to these factors and based on experience, AI can be trained to predict possible ambush sites.
Every ambush is associated with certain preparations. At this stage in the development of science, armed fighters at a certain point in space cannot yet materialize out of nowhere, unlike distant and very distant relatives when dividing the inheritance of the deceased or funny rear characters who check their combat readiness.
Heavy weapons and ammunition are brought in by vehicles, while preparing an ambush, certain earthworks can be performed, and these actions leave traces behind them. The technique leaves a track and a thermal footprint on the surface of the earth, earthworks are visible from the air. And if we combine the data of ambush location patterns and indirect signs in the form of traces, then it is possible to predict possible ambushes with some certainty. To train AI in finding such places, you can take the available data on ambushes that the enemy used. And on their basis to train AI.
When we know the weapons and their capabilities used to organize ambushes, the patterns in which ambushes are organized, we can expect them to appear in a specific place with some certainty and act in advance. Process a possible place in advance so as not to tempt fate, and keep an eye on it just in case.
To some, this whole idea with patterns of behavior and forecasting may seem like naive fantasy and an impossible idea. Every second around the world, websites and search bots collect statistics on user behavior on websites and in mobile applications. It would seem, what is the use of what is there, how many times the user clicked and where did the link go?
True, on the basis of this data, analytical companies build a digital user profile for subsequent sale to advertising or marketing companies. And those based on these models build their shares and implement strategies. IT giants are practically government organizations, they can share a digital profile with a user's social graph with their beneficiary.
Just before the start of the Sochi Olympics in decent England there was a small scandal. One chain supermarket, following the shopping of one young girl, sent home a catalog of products for pregnant women and offers with discounts on products for expectant mothers. The parents of this high school student were seriously excited and angry, they went to sort out the desecrated honor of their modest girl. A public scandal arose, and the showdown began.
It turned out that in the system of analysis of purchasing activity, a pattern was triggered that is typical for women who find themselves in a position. We all know perfectly well that at such moments the taste, nutritional and behavioral patterns of women change. Here, a system was trained on them, and, as it turned out, the system is much more accurate than parental control. Who cares - the schoolgirl graduated from high school in the status of a young mother.
Now it's time to think about tanks.
Do it somewhere. Probably, there are no exact figures to understand how many tanks were destroyed in tank battles, and how many were destroyed by ATGM crews. Perhaps the percentage of those shot down from anti-tank systems is not small, but not only tanks get from these calculations. This is a very formidable weapon, despite its small size.
As I wrote above, the sites of many ambushes can be predicted with varying degrees of certainty and checked for accuracy using artillery or the tank guns themselves. Maybe aviation help. Or maybe just the crew will not climb there, knowing the potential danger.
3. Patterns of operation of communication devices
Satellites have long been able to listen to conversations on the ground.
Prior to Gorbachev's rise to the presidency of the USSR, imported spy satellites had the ability to listen in on land-based telephone conversations. Well, those with a disk dialer, for those who remember. Now few people use wired phones with push-button dialing, most have switched to cell phones that work via radio. Our army, as far as possible, tries to keep up with the times, and gradually, thanks to cheap radio stations from Ali, it is switching from wired communications to radio. The enemy is using with might and main modern imported means of communication with fantastic capabilities by our standards.
We cannot influence the supply of modern means of communication. For the most part, you don't need much. One can benefit from such a deep penetration of foreign communications. Well, firstly, to distinguish - where is your own, where is someone else's. Where it is lilac and miserable, then ours is toiling, and where it stably jumps over frequencies and maintains the availability of the communication channel with all its might, therefore, not ours.
According to the patterns of operation of communication facilities, it is possible to determine where are ours, where are strangers, and thereby supplement the existing picture from the same observation satellites.
In addition to the patterns of communication means, there are patterns of using these tools. During the offensive, one can identify some patterns of using means of communication, others during defense, and still others for ambushes. Preparatory situations for this all also fit into certain patterns. It is not necessary to decipher the contents of the conversation. With even simple encryption, this is a lengthy operation. It is enough to observe the means of communication and the patterns of their use.
The notorious US Internet traffic tracking system "Prisma" did not decrypt the data. It simply correlated data about who, to whom, when sent a message, and the size of this message. When there are several dozen such messages, they are of no use as from a goat's milk. But when there are thousands of such messages, it is already possible to build fairly clear assumptions. Here, as in quantum mechanics, we have a lot of random events and, when a sufficient number of them are collected, we can make certain statements. That is why in government communication channels, when a communication session is terminated, pink noise or recorded meaningless snippets of phrases are fed into the channel.
Many things and phenomena can be digitized, patterns of behavior can be identified and, based on them, work ahead of the curve. The same applies to the enemy and his actions. There are also people from blood, flesh, personal problems, certain cultural customs and peculiarities of thinking, as a result - peculiarities of behavior. These features can and should be used.
4. Guidance systems
Earlier I wrote about the use of kinetic weapons launched from spacecraft to combat large aircraft and swimming vehicles. Many should have had a natural desire to put a curb handle or a crooked key to their temples and twist it well. It is quite natural if the control of such devices is carried out in the old fashioned way with high delays, costs and mandatory errors in the execution of the human factor. If an order can be ambiguous, it is sure to be misunderstood. Murphy's laws work great in combat conditions.
Any of the most modern and sophisticated transport aircraft cannot make a quantum leap and leave the space-time continuum in an unknown direction. Such feints are usually subject to budgets and wives who have seized on their husband's salary card. So, all possible states of an airliner are limited by certain boundaries in the phase space of states. He is able to circle as he likes and do aerobatics available to him, only they fit into the models of possible behavior, which are limited by the phase portrait of this aircraft, and therefore are predictable. Unless a higher power from outer space helps him.
With a fairly high probability, you can predict where the board will be in five, six, ten, fifteen minutes, half an hour. The transport worker has much fewer initial conditions describing its possible behavior compared to weather conditions. Forecasters seemed to have mastered making more or less accurate weather forecasts for the day ahead and almost approached the shamans in this field.
Returning to the transport workers in the sky, based on the initial data, we can calculate the optimal moment for launching a pebble with greetings and best wishes on the first space mission. Or on the second.
Here a large transport worker took off, gained altitude, took up its echelon. Where can he go, what will the crew perform so suddenly? Give up on the Seychelles, as ours once amused? It is unlikely. Either fall through the ground or turn back. Calculating the probabilistic trajectory of a transporter without any AI is not such a difficult task as to cause a combinatorial explosion. The possible states of the liner on the basis of its phase portrait in space are known with a certain accuracy, and on the basis of these data it is possible to choose a suitable spacecraft from which respect and respect will be sent down at one or another space speed.
In the event that a space hotel is discovered, and sooner or later everything will come to this, a transporter or a large long-range bomber has nowhere to go. Jumping from one echelon to another is pointless. A blank at a speed of 10 km / s will not play a special role, that the board will sharply drop the height from the conditional 5 m to 000 m.
Well, two seconds longer will fly. Trying to sharply maneuver and twist the loops is also not an option. We must think that it will be more dangerous for him: when a blank flies into him from above or the crew tries to create Pugachev's cobra. In addition, such aircraft fly in an area limited by their air defense system and sometimes follow each other, and for these reasons they do not have such room to maneuver. If he escapes outside his own air defense system, he can easily and warmly be met by a completely different air defense system.
Of course, this is possible with a sufficiently large number of spacecraft in orbit. If their number is comparable to the number of UAVs in our army, it is not necessary to rely on operational detection, and even more so on intercepting a target on Earth. In addition, it is necessary to take into account possible emergencies that simply love to happen to our spacecraft, and keep the satellite constellation in excess. And it is very desirable that the filling of the spacecraft be on a modern elemental base, and not from what was lying around in the warehouse.
5. Serious scientific work
I am well aware that my writing is fantastic, at times counterintuitive and mostly naive. Only more educated and literate people did not sit idly by and defended doctoral dissertations on the topic. If you still have strength left after reading, you can search for a work available in the public domain called "An Unsupervised Machine Learning Tactical Inference Generator". There are more serious things described than here. In general, D. Ezra Sidran is quite a prolific author on this topic.
Afterword
It's probably a tradition here. In which case, make historical references to the times of the world wars and give examples of the heroism, courage and unpretentiousness of the soldiers of those times. For everyone who wants to do this again in the comments, I ask you to recall the school curriculum of the Russian language and literature with the wonderful poem “Borodino” by M. Yu. Lermontov. If in those days he wrote for his contemporaries “heroes are not you”, what can we say about the current generation? As soon as you feel like writing about how it was before, read the beginning of the poem "Borodino" and think about these lines.
For example, I can tell a story about grandfather Vanya (a veteran of the Great Patriotic War, Ivan Dmitrievich). On a dare, he took the M12 lerk in his hand and cut a thread on a steel bar without a wrench and all sorts of adaptations. Such a man had power in his hands. The current generation of young people with great difficulty imagines what a lerka is and why a tap is needed.
In the commissariat, now the military commissar, in the presence of his mother, gives the recruit two sim cards and a bank card so that parental chats in instant messengers and groups of unfortunate people in social networks sleep peacefully. Therefore, I express my thoughts based on modern realities. And they are such that some heroes of cyberspace can hardly build communication in real life. A kind of pronounced introverts with the habits of a sociopath in one bottle. Are there commanders among the readers who can compare the conscription of the early 2000s and the modern conscription? Tell me, which are more frostbitten?
Information