Who so "wants to cry"?
Let's talk in more detail about the damage done to one or another country and the security / insecurity of modern networks from such and other cyber attacks.
So, the WannaCry virus began 12 massive blows in May. Distribution activity is exponentially. The countries of the European Union, the USA, Canada, the Russian Federation, China, Japan, South Korea, Australia, India, Saudi Arabia, Turkey, Iran, Israel, and a number of Latin American countries were under attack. WannaCry even got to Iceland and Mongolia.
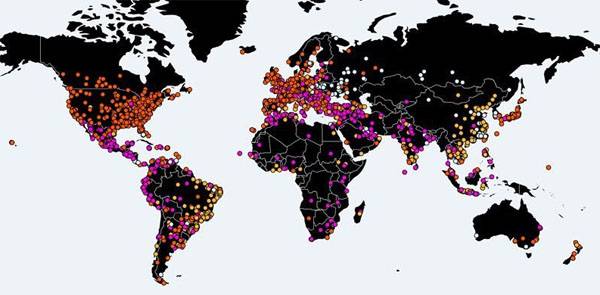
According to the latest data, the virus attack either bypassed or barely affected such countries as Turkmenistan, Kazakhstan, Afghanistan, Tajikistan, Papua New Guinea, North Korea and a number of African states such as Somalia, Chad, Mali, Botswana, etc. For rare exceptions in the list are countries in which the Internet is extremely underdeveloped, plus - a small number of computers and systems based on operating systems from the American company Microsoft. In general, the virus made its way to where there is, what to profit. Separate countries from such a list are still ignored.
The attacks were: the British healthcare system (a virus hit computers in nearly fifty British hospitals, and they were unable to perform electronic patient registration and remote consulting), the largest German railway operator Deutsche Bahn, the Spanish communication company Telefonica, US banks and cellular operators, Turkish companies tourism sector and many others.
It should be recalled that the May version of the encryption virus is a modification of the virus that has already managed to do a lot of dirty work on the Internet in the winter. To be fair, then the activity of the extortion coder was an order of magnitude lower. But, as you know, everything flows, everything changes, the virus has changed, having “expanded” so that a few countries did not come under its blow.
By the way, immediately after the virus got into the network, former US intelligence officer Edward Snowden announced that the virus-cipher virus had left the US National Security Agency laboratory at the time. In other words, they created a destructive computer program that gains access to personal computers and mobile devices, precisely in the depths of the special services of the United States.
The first thoughts about who launched WannaCry into the network were noted by representatives of the American and British political elites. And these considerations in the light of the latest hysteria associated with the ubiquitous Russian hackers have not gone further than the regular statements about the "guilt of Russia". They accused Russia again, despite the fact that Russia was among the countries that the virus attacked most actively and methodically. However, a couple of days have passed since the activation of the encryption virus, and a new version is being discussed in Western media. Moreover, this version, apparently, appeared after the West had carefully studied the map of “strikes” inflicted by WannaCry. Seeing that the virus did not damage the DPRK, they decided to hang all the "viral" dogs on Pyongyang and allegedly on some hacker group affiliated with Pyongyang. Even the name was reported - Lazarus Group, which was previously accused of attacks on the Sony network in 2014, as well as on the National Bank of Bangladesh, which last year lost approximately 80 million dollars after the hacker strike.
The virus affected computers and systems based on Windows OS, which did not pass through the updates. The largest number of such computers is in Russia and India (from all large countries with a large number of personal computers). This is exactly what experts at F-Secure, an anti-virus software company, claim. Representatives of the company say that the computers that run on Windows XP OS suffered the most damage from the virus. This system was no longer serviced by Microsoft some time ago, and no updates for it have been released for a long time. In connection with the activation of a virus that strikes non-upgraded operating systems, Microsoft was forced to urgently release several so-called patches (additions to make changes to certain system files) even for Ex-Pi.
However, it was not this that stopped the spread of the virus, but the work of British IT specialists; at least that's what is stated in news agency reports. One of them conducts online activities under the nickname of his microblog @MalvareTechBlog. He said that he had found some email address in the virus code (here is its full view: iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.com), to which the virus is constantly addressed. Next, @MalvareTechBlog and a colleague named Darian Hass registered the site with the same address name. This led to a significant decrease in the activity of the virus, which, according to these British, may soon recover due to the change of addresses of the circulation of virus components by cybercriminals.
What attracts attention? Despite the tremendous hype raised by "antivirus" companies and the Western media, the real economic damage from WannaCry is not as significant as one would expect. It turns out that extorting the banner that appears from the screen of an infected PC, from 300 to 600 dollars, the attackers were able to “get hold of” about 50 thousand dollars. As theft, it seems to be a considerable amount, but clearly not in the case when it comes to infecting computers almost all over the world.
This suggests that in fact those who launched WannaCry set themselves a slightly different task than dislodging funds from users. It’s too small for a hacker group that the West stubbornly connects with North Korea. Unless, of course, you convince yourself that in this way Kim III was trying to make money on a new service jacket for himself and on a supply of solyary for a ballistic missile wheeled tractor ...
It is important that the computer managed to spread to 150 states of the world and at the same time actively tried to “knock” on the PC of large companies, ministries and departments. In some places, they say, I got through ... Against this background, the dramatically increased number of user requests for MS Windows updates, as well as the equally dramatic increase in the number of downloads of antivirus programs and purchases of keys to them, attracts attention. If cybercriminals earned, as they say, 50 thousand dollars on gullible users, how much did Microsoft earn with anti-virus advocates? .. This information is not made public. Maybe with the intention that users suddenly wondered who it all was more profitable.
- Alexei Volodin
Information